The title of this post says it all; and it’s all over the news. NICE Systems, Ltd, an Israeli company, does backend call-center work for Verizon. In a project with Verizon, a cloud server from Amazon AWS S3 was used to store call center data in an effort to improve customer service. However, that data contained customer phone numbers, voice recognition snippets, and PIN numbers associated with the accounts.
The AWS S3 server was not secured; it was publically accessible. The databases (zip files) and the terrabytes of data therein could be accessed by anyone bunbling or stumbling across the S3 server’s URL.
We know that there were over 14 million records on that server. Verizon says it affected 6 million customers. It’s important to know that nobody knows who else might have pilfered that data. Accountability is the Cloud’s biggest failing. Neither Verizon or NICE Systems actually own, or have physical access to, the server.
So, what can be worse? The server was discovered onn June 8th by UpGuard’s cyber risk research director, Chris Vickery . UpGuard is a Cyber-Security firm that started up in Austrailia, then moved to the US. They have products to manage “Configuration Drift“, DevOps, and Risk Management. UpGuard notified Verizon of the unsecured data on June 13th. On June 22, 2017, 9 days later, Verizon secured the server.
So, what can a hacker do with a phone number and corresponding PIN? Hijack your phone account, much to your surprise. Oh, and so many 2FA systems use your cellphone for authentication purposes. Heck, you can even get password reset links sent to your phone. It’s not a good thing. At a minimum, change your Verizon account PIN number now. It’s probably a good idea to change the passwords associated with any applications that are on your phone for good measure.
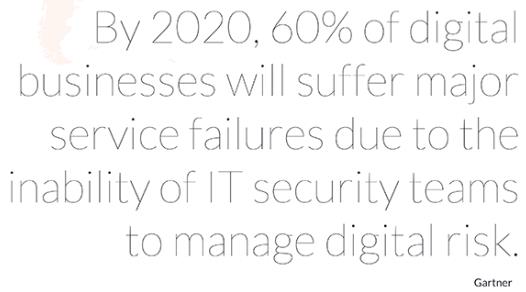
UpGuard’s disclosure report can be found here. They present an interesting graphic:
There are continuing lessons to be learned here:
- Don’t put stuff in the cloud that you can’t affort to lose.
- Where there is no physical control, there is no security.
- Always supervise your service partners. Where’s your data?
As Dan O’Sullivan, an analyst for UpGuard quipped, “Verizon did not own the server that was involved here, but it will own the consequences.”