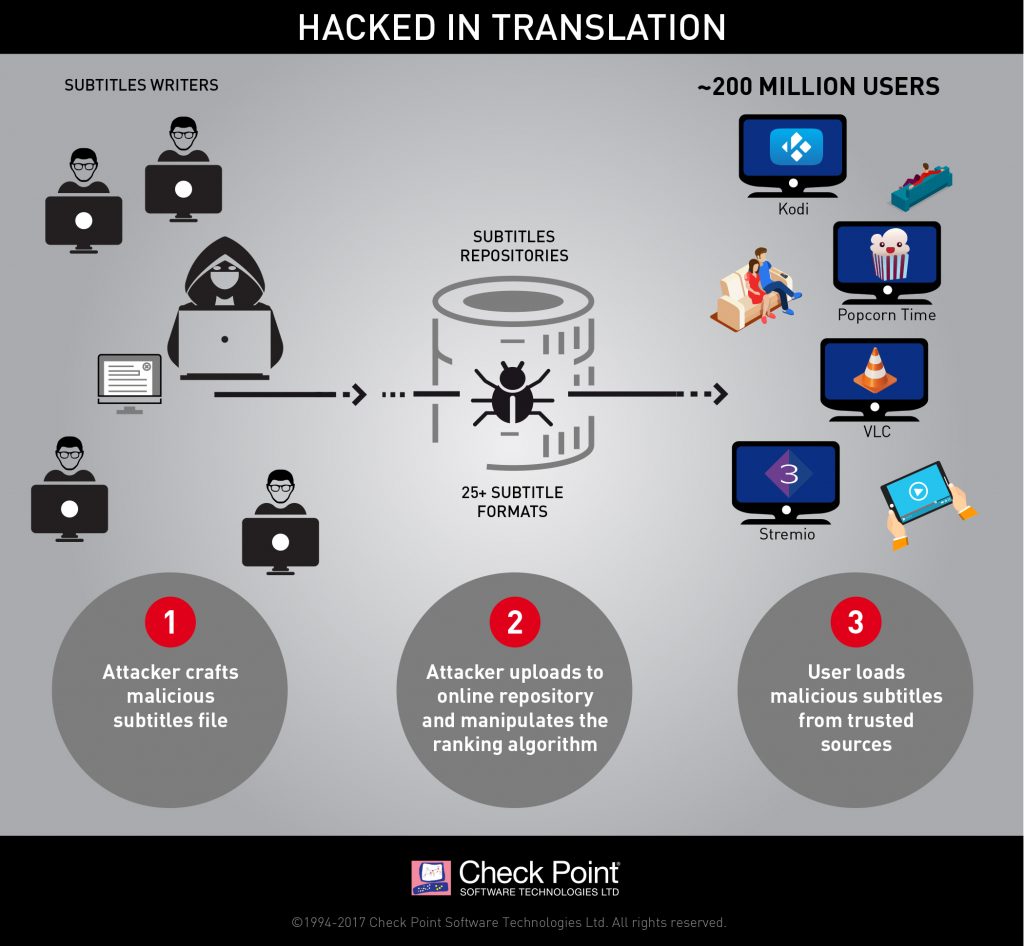
Check Point Software Technologies has uncovered vulnerabilities in the processing of Subtitles with the four most popular movie players for Windows and Linux systems:
- VLC
- Kodi
- Popcorn-Time
- Stream.io
Hackers can exploit Subtitle ranking algorithms and allow exploited subtitles to be delivered first. The instant the subtitle is loaded, the hacker is able to perform Remote Code Execution (RCE) and take complete control over the target PC.
Check Point’s post on this issue is here.
All of these vendors have fixes available. You should upgrade these programs immediately.